PRODUCTS
-
Inductive proximity sensor
- Square Proximity Sensor
- High temperature proximity sensor
- Low temperature proximity sensor
- ring proximity sensor
- Standard inductive proximity sensor
- Ultra Small inductive proximity sensor
- Long Distance Proximity Sensor
- Corrosion resistant proximity sensor
- metal face proximity sensor
- high pressure proximity sensor
- Analog proximity sensor
- namur proximity sensor
-
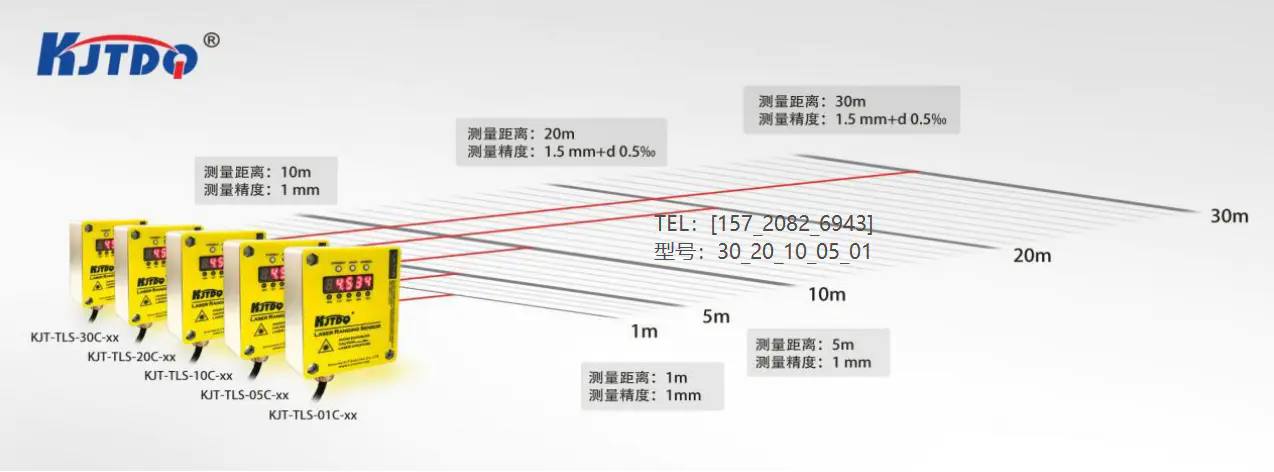
Laser sensor
- Explosion-proof laser distance measurement sensor
- Laser distance measurement module
- Intelligent driving system
- Laser hot and cold metal sensor
- Laser liquid level sensor
- TOF laser photoelectric sensor
- High-precision displacement sensor
- Amplifier built-in TOF laser sensor
- High frequency laser distance sensor
- High-precision laser distance sensor
- Capacitive proximity sensor
-
Photoelectric sensor
- Traffic collision protection device
- Square series
- Optical fiber
- Fiber amplifier
- standard series
- Cylindrical Photoelectric sensor
- Slot type Photoelectric sensor
- Square type Photoelectric sensor
- Long range Photoelectric sensor
- Optical fiber sensor
- High temperature Photoelectric sensor
- Laser Photoelectric sensor
- Color mark sensor
- Small photoelectric sensor
- Safety light curtain
- Megnetic Sensor
- Speed Sensor
- Textile special sensor
- Limit switch
- Vibration Sensor
- Measuring sensor
- Wireless sensor
- Conveyor belt protection devices
- Sensor accessories
road map approach for sensor network assisted navigation in dynamic environments.
by:KJTDQ
2020-05-11
This paper introduces a wireless sensor network (WSN)
It is usually composed of autonomous sensors distributed in topology for monitoring physical or environmental conditions.
Wireless sensor networks have a good application prospect in real-time monitoring.
They are used for habitat monitoring, personnel tracking, road navigation, battlefield monitoring, and structural monitoring.
In recent years, by eliminating all the obstacles that ordinary users may encounter, sensors that are most suitable for navigation purposes have been found.
There are many successful ways to solve navigation problems using wireless sensor networks, reducing costs and energy consumption.
Most existing methods require a location or require a pre-user
Know where he is (Zhu, Y. , 2009; Hartl, G. , B. Li, 2004).
In addition, the user must be notified in advance when a dangerous alarm is issued in a safe area.
It needs to update the roadmap for node status.
The time interval spent updating the routing path in the sensor network must be minimal (Sommer, C. , 2011).
In addition to this, when the user is booted on the roadmap, the sensor should track the activity performance of the neighbor node.
If these problems are not solved, the user query will be interrupted due to the wrong behavior of the sensor node.
The proposed framework is designed based on the road map (RM)
Methods that do not rely on location information.
The user queries the navigation system of the specified target node.
The roadmap consists of static sensor nodes connected via a dynamic path (Choset, H. , K. Nagatani, 2011;
Mr. batacharia, S. , 2006).
There can be several changes on the path connecting the sensor node.
These changes are caused by factors such as possible dangerous areas and sensor node failures in sensor networks.
This threatens human security in navigation.
The RM approach is capable of responding to the dynamics of hazardous areas.
In addition, the distributed features greatly reduce the network overhead. I.
Problem specification: Distributed sensor networks are implemented by navigation in case of emergency.
We consider navigating the human scene on the road map in case of emergency, with several dangerous areas that threaten the safety of human life, defective nodes and crowded nodes.
The distributed sensor network framework manages request and response messages from users.
User queries are directed to a roadmap consisting of sensor nodes.
The actual route is determined by the navigation path block that exists in the architecture framework.
It contains navigation algorithms that determine the nearest jump distance.
The emergency dynamics will be handled separately, thus updating the status to the roadmap.
There are three main requirements for navigation systems.
* It is required to ensure the security of the selected route path.
It should be as far away from dangerous areas as possible.
* Provide congestion-free routing paths in high traffic situations.
* The navigation protocol should be scalable. II.
Sensor Network navigation framework: the design of distributed sensor navigation system includes six components.
They are building a roadmap to guide navigation on the roadmap, detect dangerous areas, detect fault nodes, congestion control mechanisms and improve routing efficiency.
Update roadmap in event-
The driving concept of any change in sensor node behavior. A.
Build roadmap: the topology of the Distributed Sensor framework is deployed by the specified grid size (Choset, H. , K. Nagatani, 2011).
In our proposed work, milestones are built in the grid structure.
The node that marks the end of the network is called a boundary node.
The area on the road map is divided into three main areas, namely: the safe area suitable for navigation, the dangerous area where the alarm sensor is found, and the fault node with path indication.
All sensor nodes are deployed within equal distances.
Initially, the transmission range remains the same for all sensor nodes.
The basic framework is limited to specific areas, so areas outside the framework are clearly considered dangerous. B.
Guide navigation on the roadmap: a successful navigation protocol should provide the shortest possible secure path.
In this module, we design the path between sensor nodes.
The node connection is calculated by calculating the minimum distance (Buragohain, C. , 2006).
So there can be 3 to 4 neighbors per node.
The framework in which the user requests a navigation route by specifying the target node.
Then, the flood information with the target node comes from the source.
Complete navigation path is not obtained immediately;
Instead, the sequential path is determined after the node is reached.
The RM method eliminates the situation of being hit in a dangerous area.
Therefore, by exchanging flood information locally from one node to another, the framework can know all security nodes at any time. C.
Detection of dangerous areas: dangerous areas are limited at any time.
There are several basic types of changes in dangerous areas, including emergence, expansion, reduction and reduction.
The expansion of dangerous areas may transfer several safe areas to dangerous areas.
In our proposed work, dangerous nodes are randomly selected.
In real time, the alarm sensor will trigger the LED light to red.
This makes it easy to identify the normal sensors and alarm sensors in the roadmap area.
If the sensor node is in a safe or hazardous area, update itself from the sensor data.
Usually the sensor in the safe area triggers the flag value to 0, and the sensor in the dangerous area triggers the flag value to 1 (Li, M. , 2013).
Any changes in the roadmap area are checked and updated to sensor memory on a regular basis.
Enter the standard temperature and pressure values into the sensor processing unit.
The node switches from the security area to the danger area based on the received sensing information. D.
Fault node detection: since we provide dynamic path updates, all sensor nodes should be active to guide navigation.
Its neighbor node receives a Hello packet message to check if the sensor node is alive.
If any sensor node in the network does not receive a hello packet message from a neighbor, then it is called dead.
In this way, the fault node is easily identified and isolated from the navigation.
The fault node cannot be idle all the time.
After a small iteration, it can be fixed by deploying a new sensor node.
In this case, the update dynamics come in handy and the fault node resumes its functionality. E.
Congestion control and traffic redirection: sensor nodes can only process a specified number of queries at the same time.
If this happens when more vehicles choose the same path, then sensor nodes may handle more queries that cause congestion.
It reduces the response time and battery power of the sensor node.
Therefore, the congestion control mechanism (Wan, C. , 2005)is imposed.
We introduce Aq values that specify the number of query vehicles that the path can support within a specific time interval.
The selection of this value makes the sensor node considered to be in a state of congestion when its Aq reaches 80% usage.
All sensor nodes are well identified before maximum congestion is reached.
After the congestion node is determined, the vehicle close to the node should be re-connected
Points to its adjacent nodes.
The traffic redirection principle is achieved by using the redirect bit in the network layer header. F.
Improve route efficiency: the way to select the selected navigation route is to give the shortest path without entering any dangerous field.
On the Road trunk, maximize the path in the specified direction to the minimum distance in the dangerous area.
If the shortest distance is greater than the distance in the dangerous area, then this point is said to be in the safest place.
In the presence of obstacles, the sensor cannot always give the shortest path;
In an emergency.
It still provides users with guaranteed security paths with minimal network overhead. III.
Simulation results: a distributed navigation framework is simulated in OMNeT 4. 3 (Kopke, M. , 2008).
Initially, the simulation area was built statically and remained unchanged throughout the simulation cycle.
Deploy sensor nodes in a matrix structure.
The battery power and transmission range of all sensor nodes have the same value.
Establish a routing table at the network layer to determine the next hop.
The number of dangerous areas is selected from 1 to 6.
Therefore, the total dangerous area is 5-at any time-
6% of the simulated area.
The update interval is set to 20 s, where the sensor network faces changes related to the state of the node.
Users are always away from dangerous areas.
The following table gives a brief detail of the simulated environment: IV.
Performance Analysis: to measure the effectiveness of our navigation system, we consider some performance metrics.
The RM method is compared with two existing systems in terms of four parameters.
One is the skeleton diagram (SG)(Buragohain, C. , 2006)
A protocol based on greedy geographic solutions and exhaustive search.
Although it gives the optimal path length, this method is affected by the cost of communication.
Other approaches are potential areas (PF)(Li, Q. and D. Rus, 2005)
Protocol-based approach.
This method is completely focused on finding a potential value distance of 1/d (2)
Each route path.
The evaluation is done by changing the network size from 400 to 1000.
Compared with these methods, the performance measures are as follows: A.
Minimum distance to danger: for a safe navigation path, the planned route should be the maximum possible distance from the hazardous area.
: The performance ratio for calculating the minimum distance from the hazard is given in d/dOPT.
Let d indicate the minimum distance from the path actually planned to the nearest dangerous area.
DOPT means that the shortest path of the point in the dangerous area is not considered.
Therefore, it is observed that dOPT should be selected in order to maximize d in the case.
Due to the low probability of getting into danger, this ratio should be high.
SG and PF methods are compared with the proposed roadmap system in terms of network size.
The performance ratio of SG is 0.
The performance ratio of 4 to PF is 0. 6 (
These values are from (Li, M. , 2013)).
The road map method is given 0.
The performance ratio is quite high compared to existing methods.
Thus ensuring the security of guiding users. B.
Shortest path: all types of users want to use the shortest path for any navigation system.
Evaluate path efficiency by recording the path length of each query (Veltri, G. , 2003).
Despite the obstacles, the minimum jump distance should be selected to reach the destination.
In this simulation, 10 users navigate along the road map with few hazard and fault nodes.
In the RM method, even if there is an obstacle path, the possibility of giving the shortest path is increased.
The planned route may not always give the shortest route;
Because the biggest goal of navigation is not to take a dangerous road, but to maintain the shortest path length (Sommer, C. , 2011).
However, given the hazard and fault node area, the chosen path is considered to be the shortest.
Relatively small performance;
The path is small.
Calculate the shortest distance per route path using jump distance. C.
Path Traversal: Path Traversal is the average navigation time spent by mobile users to reach their destination.
Users travel at different mobile speeds.
Since the high speed in the forest area is considered dangerous, the movement speed of all internal users is limited to 25 m/s. Figure 5.
5 describes the time to navigate an internal user by changing the movement speed of the internal user according to the update frequency.
We infer that a lower frequency of updates can lead to longer navigation times.
The frequent changes in the network topology will affect the transmission and reception of packets, resulting in traffic in the network.
So, for the best navigation, a larger 20s update interval was used. Figure.
7 describes the path traversal time relative to the number of users.
The number of users is proportional to the navigation time.
Keep the percentage of dangerous areas unchanged and record the following values.
Since dynamic routing paths are provided to all users, the navigation time may vary in different instance VI.
Conclusion: In this study, a distributed sensor network framework for navigating users in emergency situations is proposed.
Wireless sensor networks pave an effective way for users to provide the best path by sensing environmental conditions.
Our approach can overcome this emergency without relying on location information.
It enhances the existing navigation system and solves the more prone node failures and congestion problems in wireless sensor networks.
The update mechanism of periodic time interval is used to solve the change of dangerous area and node state, which makes the sensor network more reliable for dynamic users.
In order to verify the performance of the framework, the network size is increased.
Since high-performance sensors are users, the power consumption is clearly quite high compared to existing methods.
In order to reduce power consumption, enhancements can be made in the future.
Overall, network overhead is relatively low to a large extent.
Navigate the network and users in the shortest path to ensure security.
Article information article history: Received on October 12, 2014, revised December 26, 2014, received on January 1, 2015, accepted online reference on February 25, 2015, Bhattacharya, N. Atay, G. Alankus, C. Lu, O. B. Bayazit and G. Roman, 2006.
\"Route Map Query for sensor network-assisted navigation in dynamic environment\", Proc.
The second IEEE International Conference
Distributed computing in sensor systems (DCOSS).
Buragohain, C. , D. Agarwal and S. Suri, 2006.
Distributed navigation algorithm for sensor networks\"IEEE INFOCOM. Choset, H. , K. Nagatani, 2011.
\"Simultaneous mapping of topology (SLAM)
: Precise localization without explicit localization.
IEEE transaction son robotics and automation, 17 (2). Edison, P. , T.
Himafis, Freitas, F.
Ivar, Neto, Carlos. Pereira, A.
Flavio in R in Mora moreWagner, T. Larsson, 2011.
\"Handle the failure of static sensor nodes in wireless sensor networks using mobile sensors,\" Proc.
Workshop on the International Conference on Advanced information networks and applications. Hartl, G. , B. Li, 2004.
\"Wireless Sensor Network loss inference based on data aggregation\", Proc. ACM 1-58113-846, IPSN. Kolushev, F. A. and A. A. Bogdanov, 1999. \"Multi-
Agent optimal path planning for mobile robot with obstacle environment.
The Third International Conference on the commemoration of Andre elshaev.
Views of systems Informatics (PSI). Kopke, M. , K. Swigulski, D. Wessel, P. T. Willkomm, T. E. V.
Klein hanniffW. Parker, H. S. Visserm S.
2008, Valentine, Richter.
Proc simulates wireless and mobile networks in OMNeT. Intl.
OMNeT workshop, March. Li, M. , Y. Liu, J. Wang and Z. Yang, 2013.
\"Sensor Network navigation without location\", Proc.
IEEE Transactions on Parallel and Distributed Systems, 24 (7). Li, Q. and D. Rus, 2005.
\"Navigation protocol in sensor network\", ACM Trans.
Sensor Network, 2005. Mao, X. , X. Xu, S. Tang, X. Li, 2010.
\"Provide and find k-road-
Effective coverage in wireless sensor networks.
Wireless communication and mobile computing. Ravindra, N. , N. P.
Duch, sardwade, 2012.
\"Sensor node failure or fault detection in wireless sensor networks\", Proc. ACEEEInt. J.
About communication, 03 (01). Sommer, C. , R. German, F. Dressler, 2011.
\"Two-way coupling network and road traffic simulation for improved IVC analysis,\" Proc.
IEEE Transactions on Mobile Computing, 10 (1). Veltri, G. , Q. Huang, G. Qu, M.
Potkonjak, 2003.
\"Minimum and maximum exposure path algorithm for wireless embedded sensor networks\", Proc. SenSys\'03, 5-7, 2003, ACM 1-58113-707-9. Wan, C. , S. B. Eisenman, A. T. Campbell and J.
2005 Croft
Rainbow straw: overloaded traffic management used many times
\"Proc\" radio virtual receiver. ACM Int\'l Conf.
Embedded Network SystemSenSys). Wang, Y. , R. Tan, G. Xing, J. Wang and X. Tan, 2012. \"Accuracy-
Analysis of the perceived aquatic diffusion process using a robotic sensor network, \"Proc. Int\'l Conf.
Information Processing in Sensor Networks (IPSN). Zhu, Y. , Y. Liu and L. M. Ni, 2009.
\"Optimize event detection under low load-
Loop sensor network.
18: 241-wireless network255. (1)G. Santhi and (2)R.
Cavita Kumar (1)
Assistant Professor, Department of Information Technology, School of Engineering, Pondick, India. (2)
CSE, School of Engineering, Pondicherry, India.
Author: G.
Santhi, assistant professor, information technology department, Pondicherry Institute of Engineering, India. E-
Mail: shanthikarthikeyan @ pecedu.
It is usually composed of autonomous sensors distributed in topology for monitoring physical or environmental conditions.
Wireless sensor networks have a good application prospect in real-time monitoring.
They are used for habitat monitoring, personnel tracking, road navigation, battlefield monitoring, and structural monitoring.
In recent years, by eliminating all the obstacles that ordinary users may encounter, sensors that are most suitable for navigation purposes have been found.
There are many successful ways to solve navigation problems using wireless sensor networks, reducing costs and energy consumption.
Most existing methods require a location or require a pre-user
Know where he is (Zhu, Y. , 2009; Hartl, G. , B. Li, 2004).
In addition, the user must be notified in advance when a dangerous alarm is issued in a safe area.
It needs to update the roadmap for node status.
The time interval spent updating the routing path in the sensor network must be minimal (Sommer, C. , 2011).
In addition to this, when the user is booted on the roadmap, the sensor should track the activity performance of the neighbor node.
If these problems are not solved, the user query will be interrupted due to the wrong behavior of the sensor node.
The proposed framework is designed based on the road map (RM)
Methods that do not rely on location information.
The user queries the navigation system of the specified target node.
The roadmap consists of static sensor nodes connected via a dynamic path (Choset, H. , K. Nagatani, 2011;
Mr. batacharia, S. , 2006).
There can be several changes on the path connecting the sensor node.
These changes are caused by factors such as possible dangerous areas and sensor node failures in sensor networks.
This threatens human security in navigation.
The RM approach is capable of responding to the dynamics of hazardous areas.
In addition, the distributed features greatly reduce the network overhead. I.
Problem specification: Distributed sensor networks are implemented by navigation in case of emergency.
We consider navigating the human scene on the road map in case of emergency, with several dangerous areas that threaten the safety of human life, defective nodes and crowded nodes.
The distributed sensor network framework manages request and response messages from users.
User queries are directed to a roadmap consisting of sensor nodes.
The actual route is determined by the navigation path block that exists in the architecture framework.
It contains navigation algorithms that determine the nearest jump distance.
The emergency dynamics will be handled separately, thus updating the status to the roadmap.
There are three main requirements for navigation systems.
* It is required to ensure the security of the selected route path.
It should be as far away from dangerous areas as possible.
* Provide congestion-free routing paths in high traffic situations.
* The navigation protocol should be scalable. II.
Sensor Network navigation framework: the design of distributed sensor navigation system includes six components.
They are building a roadmap to guide navigation on the roadmap, detect dangerous areas, detect fault nodes, congestion control mechanisms and improve routing efficiency.
Update roadmap in event-
The driving concept of any change in sensor node behavior. A.
Build roadmap: the topology of the Distributed Sensor framework is deployed by the specified grid size (Choset, H. , K. Nagatani, 2011).
In our proposed work, milestones are built in the grid structure.
The node that marks the end of the network is called a boundary node.
The area on the road map is divided into three main areas, namely: the safe area suitable for navigation, the dangerous area where the alarm sensor is found, and the fault node with path indication.
All sensor nodes are deployed within equal distances.
Initially, the transmission range remains the same for all sensor nodes.
The basic framework is limited to specific areas, so areas outside the framework are clearly considered dangerous. B.
Guide navigation on the roadmap: a successful navigation protocol should provide the shortest possible secure path.
In this module, we design the path between sensor nodes.
The node connection is calculated by calculating the minimum distance (Buragohain, C. , 2006).
So there can be 3 to 4 neighbors per node.
The framework in which the user requests a navigation route by specifying the target node.
Then, the flood information with the target node comes from the source.
Complete navigation path is not obtained immediately;
Instead, the sequential path is determined after the node is reached.
The RM method eliminates the situation of being hit in a dangerous area.
Therefore, by exchanging flood information locally from one node to another, the framework can know all security nodes at any time. C.
Detection of dangerous areas: dangerous areas are limited at any time.
There are several basic types of changes in dangerous areas, including emergence, expansion, reduction and reduction.
The expansion of dangerous areas may transfer several safe areas to dangerous areas.
In our proposed work, dangerous nodes are randomly selected.
In real time, the alarm sensor will trigger the LED light to red.
This makes it easy to identify the normal sensors and alarm sensors in the roadmap area.
If the sensor node is in a safe or hazardous area, update itself from the sensor data.
Usually the sensor in the safe area triggers the flag value to 0, and the sensor in the dangerous area triggers the flag value to 1 (Li, M. , 2013).
Any changes in the roadmap area are checked and updated to sensor memory on a regular basis.
Enter the standard temperature and pressure values into the sensor processing unit.
The node switches from the security area to the danger area based on the received sensing information. D.
Fault node detection: since we provide dynamic path updates, all sensor nodes should be active to guide navigation.
Its neighbor node receives a Hello packet message to check if the sensor node is alive.
If any sensor node in the network does not receive a hello packet message from a neighbor, then it is called dead.
In this way, the fault node is easily identified and isolated from the navigation.
The fault node cannot be idle all the time.
After a small iteration, it can be fixed by deploying a new sensor node.
In this case, the update dynamics come in handy and the fault node resumes its functionality. E.
Congestion control and traffic redirection: sensor nodes can only process a specified number of queries at the same time.
If this happens when more vehicles choose the same path, then sensor nodes may handle more queries that cause congestion.
It reduces the response time and battery power of the sensor node.
Therefore, the congestion control mechanism (Wan, C. , 2005)is imposed.
We introduce Aq values that specify the number of query vehicles that the path can support within a specific time interval.
The selection of this value makes the sensor node considered to be in a state of congestion when its Aq reaches 80% usage.
All sensor nodes are well identified before maximum congestion is reached.
After the congestion node is determined, the vehicle close to the node should be re-connected
Points to its adjacent nodes.
The traffic redirection principle is achieved by using the redirect bit in the network layer header. F.
Improve route efficiency: the way to select the selected navigation route is to give the shortest path without entering any dangerous field.
On the Road trunk, maximize the path in the specified direction to the minimum distance in the dangerous area.
If the shortest distance is greater than the distance in the dangerous area, then this point is said to be in the safest place.
In the presence of obstacles, the sensor cannot always give the shortest path;
In an emergency.
It still provides users with guaranteed security paths with minimal network overhead. III.
Simulation results: a distributed navigation framework is simulated in OMNeT 4. 3 (Kopke, M. , 2008).
Initially, the simulation area was built statically and remained unchanged throughout the simulation cycle.
Deploy sensor nodes in a matrix structure.
The battery power and transmission range of all sensor nodes have the same value.
Establish a routing table at the network layer to determine the next hop.
The number of dangerous areas is selected from 1 to 6.
Therefore, the total dangerous area is 5-at any time-
6% of the simulated area.
The update interval is set to 20 s, where the sensor network faces changes related to the state of the node.
Users are always away from dangerous areas.
The following table gives a brief detail of the simulated environment: IV.
Performance Analysis: to measure the effectiveness of our navigation system, we consider some performance metrics.
The RM method is compared with two existing systems in terms of four parameters.
One is the skeleton diagram (SG)(Buragohain, C. , 2006)
A protocol based on greedy geographic solutions and exhaustive search.
Although it gives the optimal path length, this method is affected by the cost of communication.
Other approaches are potential areas (PF)(Li, Q. and D. Rus, 2005)
Protocol-based approach.
This method is completely focused on finding a potential value distance of 1/d (2)
Each route path.
The evaluation is done by changing the network size from 400 to 1000.
Compared with these methods, the performance measures are as follows: A.
Minimum distance to danger: for a safe navigation path, the planned route should be the maximum possible distance from the hazardous area.
: The performance ratio for calculating the minimum distance from the hazard is given in d/dOPT.
Let d indicate the minimum distance from the path actually planned to the nearest dangerous area.
DOPT means that the shortest path of the point in the dangerous area is not considered.
Therefore, it is observed that dOPT should be selected in order to maximize d in the case.
Due to the low probability of getting into danger, this ratio should be high.
SG and PF methods are compared with the proposed roadmap system in terms of network size.
The performance ratio of SG is 0.
The performance ratio of 4 to PF is 0. 6 (
These values are from (Li, M. , 2013)).
The road map method is given 0.
The performance ratio is quite high compared to existing methods.
Thus ensuring the security of guiding users. B.
Shortest path: all types of users want to use the shortest path for any navigation system.
Evaluate path efficiency by recording the path length of each query (Veltri, G. , 2003).
Despite the obstacles, the minimum jump distance should be selected to reach the destination.
In this simulation, 10 users navigate along the road map with few hazard and fault nodes.
In the RM method, even if there is an obstacle path, the possibility of giving the shortest path is increased.
The planned route may not always give the shortest route;
Because the biggest goal of navigation is not to take a dangerous road, but to maintain the shortest path length (Sommer, C. , 2011).
However, given the hazard and fault node area, the chosen path is considered to be the shortest.
Relatively small performance;
The path is small.
Calculate the shortest distance per route path using jump distance. C.
Path Traversal: Path Traversal is the average navigation time spent by mobile users to reach their destination.
Users travel at different mobile speeds.
Since the high speed in the forest area is considered dangerous, the movement speed of all internal users is limited to 25 m/s. Figure 5.
5 describes the time to navigate an internal user by changing the movement speed of the internal user according to the update frequency.
We infer that a lower frequency of updates can lead to longer navigation times.
The frequent changes in the network topology will affect the transmission and reception of packets, resulting in traffic in the network.
So, for the best navigation, a larger 20s update interval was used. Figure.
7 describes the path traversal time relative to the number of users.
The number of users is proportional to the navigation time.
Keep the percentage of dangerous areas unchanged and record the following values.
Since dynamic routing paths are provided to all users, the navigation time may vary in different instance VI.
Conclusion: In this study, a distributed sensor network framework for navigating users in emergency situations is proposed.
Wireless sensor networks pave an effective way for users to provide the best path by sensing environmental conditions.
Our approach can overcome this emergency without relying on location information.
It enhances the existing navigation system and solves the more prone node failures and congestion problems in wireless sensor networks.
The update mechanism of periodic time interval is used to solve the change of dangerous area and node state, which makes the sensor network more reliable for dynamic users.
In order to verify the performance of the framework, the network size is increased.
Since high-performance sensors are users, the power consumption is clearly quite high compared to existing methods.
In order to reduce power consumption, enhancements can be made in the future.
Overall, network overhead is relatively low to a large extent.
Navigate the network and users in the shortest path to ensure security.
Article information article history: Received on October 12, 2014, revised December 26, 2014, received on January 1, 2015, accepted online reference on February 25, 2015, Bhattacharya, N. Atay, G. Alankus, C. Lu, O. B. Bayazit and G. Roman, 2006.
\"Route Map Query for sensor network-assisted navigation in dynamic environment\", Proc.
The second IEEE International Conference
Distributed computing in sensor systems (DCOSS).
Buragohain, C. , D. Agarwal and S. Suri, 2006.
Distributed navigation algorithm for sensor networks\"IEEE INFOCOM. Choset, H. , K. Nagatani, 2011.
\"Simultaneous mapping of topology (SLAM)
: Precise localization without explicit localization.
IEEE transaction son robotics and automation, 17 (2). Edison, P. , T.
Himafis, Freitas, F.
Ivar, Neto, Carlos. Pereira, A.
Flavio in R in Mora moreWagner, T. Larsson, 2011.
\"Handle the failure of static sensor nodes in wireless sensor networks using mobile sensors,\" Proc.
Workshop on the International Conference on Advanced information networks and applications. Hartl, G. , B. Li, 2004.
\"Wireless Sensor Network loss inference based on data aggregation\", Proc. ACM 1-58113-846, IPSN. Kolushev, F. A. and A. A. Bogdanov, 1999. \"Multi-
Agent optimal path planning for mobile robot with obstacle environment.
The Third International Conference on the commemoration of Andre elshaev.
Views of systems Informatics (PSI). Kopke, M. , K. Swigulski, D. Wessel, P. T. Willkomm, T. E. V.
Klein hanniffW. Parker, H. S. Visserm S.
2008, Valentine, Richter.
Proc simulates wireless and mobile networks in OMNeT. Intl.
OMNeT workshop, March. Li, M. , Y. Liu, J. Wang and Z. Yang, 2013.
\"Sensor Network navigation without location\", Proc.
IEEE Transactions on Parallel and Distributed Systems, 24 (7). Li, Q. and D. Rus, 2005.
\"Navigation protocol in sensor network\", ACM Trans.
Sensor Network, 2005. Mao, X. , X. Xu, S. Tang, X. Li, 2010.
\"Provide and find k-road-
Effective coverage in wireless sensor networks.
Wireless communication and mobile computing. Ravindra, N. , N. P.
Duch, sardwade, 2012.
\"Sensor node failure or fault detection in wireless sensor networks\", Proc. ACEEEInt. J.
About communication, 03 (01). Sommer, C. , R. German, F. Dressler, 2011.
\"Two-way coupling network and road traffic simulation for improved IVC analysis,\" Proc.
IEEE Transactions on Mobile Computing, 10 (1). Veltri, G. , Q. Huang, G. Qu, M.
Potkonjak, 2003.
\"Minimum and maximum exposure path algorithm for wireless embedded sensor networks\", Proc. SenSys\'03, 5-7, 2003, ACM 1-58113-707-9. Wan, C. , S. B. Eisenman, A. T. Campbell and J.
2005 Croft
Rainbow straw: overloaded traffic management used many times
\"Proc\" radio virtual receiver. ACM Int\'l Conf.
Embedded Network SystemSenSys). Wang, Y. , R. Tan, G. Xing, J. Wang and X. Tan, 2012. \"Accuracy-
Analysis of the perceived aquatic diffusion process using a robotic sensor network, \"Proc. Int\'l Conf.
Information Processing in Sensor Networks (IPSN). Zhu, Y. , Y. Liu and L. M. Ni, 2009.
\"Optimize event detection under low load-
Loop sensor network.
18: 241-wireless network255. (1)G. Santhi and (2)R.
Cavita Kumar (1)
Assistant Professor, Department of Information Technology, School of Engineering, Pondick, India. (2)
CSE, School of Engineering, Pondicherry, India.
Author: G.
Santhi, assistant professor, information technology department, Pondicherry Institute of Engineering, India. E-
Mail: shanthikarthikeyan @ pecedu.
Custom message





















![[Good news] Nanjing Institute of Technology joins hands with Kaijit to establish an “off-campus practical education base”](https://img80002753.weyesimg.com/uploads/www.kjt-sensor.com/images/17133382885300.jpg?imageView2/2/w/1920/q/75/format/webp)










![[Good news] KJT was awarded the](https://img80002753.weyesimg.com/uploads/www.kjt-sensor.com/images/17132350274153.jpg?imageView2/2/w/1920/q/75/format/webp)
![[Invitation Letter] 2021SIA Dongguan Smart Factory Exhibition and DME Dongguan International Machine Tool Exhibition](https://img80002753.weyesimg.com/uploads/www.kjt-sensor.com/images/17132347116490.jpg?imageView2/2/w/1920/q/75/format/webp)
![[Good news] Kaijit passed the national high-tech enterprise review and certification](https://img80002753.weyesimg.com/uploads/www.kjt-sensor.com/images/17132343883285.jpg?imageView2/2/w/1920/q/75/format/webp)